tadi semasa asyik dengan bloghopping, tetiba saya rasa laptop saya slow semacam adjer. bila saya check download ngan upload testing, memang slow giler. takkan streamyx tetiba off-form plak kot.
then i restart the router cum modem. sekali not work la. bencinyaaaaa.
then got the idea of checking my task manager. i can’t even open my task manager! what the…..
apa yang berlaku neh. siapa hack aku nyer laptop plak. bila nak cuba regedit satu mende pun tak keluar.
ni dah lebey neh. cam something wrong adjer kan.
so lepas fikir 2 minutes, the best way to recover is to restart the laptop and see the effect post shutdown.
lepas restart windows. keluar plak message macam kat bawah neh.
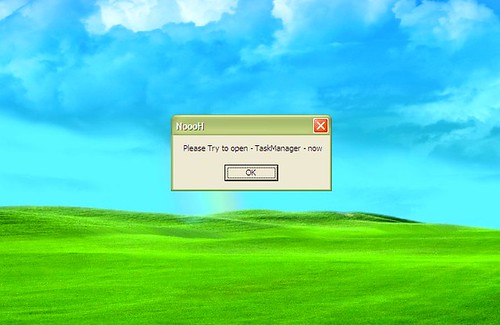
memang sah la laptop saya kena cacing. hampeh la!
terus browse internet and then need to find the removal tools the soonest possible. search punya search, saya jumpa dengan satu website yang paling berguna. website ni – ghiath computer site memang cun la kan. mamat neh siap buat satu special program yang works like NoooH worm removal tool.
W32.Alnuh is a worm that copies itself to removable drives and closes Registry Editor, Task Manager, Command Prompt and Folder Options of Windows Explorer running on English and Arabic Windows. It displays a Message Box with
Title: NoooH and
Body: Please Try to open – TaskManager – nowRisk Level: Low
Alias: W32.Alnuh
Symptoms: It closes windows of the following process
- \\cmd.exe
- Folder Options
- 32\\command.c
- Windows Task Manager
- Registry Editor
Displays a message window:
Related Files and Process:
- C:\Windows\Web\Sys.exe
apa lagi need to download la removal tool neh.
lepas download kat sini, the kena install. semua nampak cam senang. sekali masa nak install, program ask for microsoft.NET 2.0. cheh! macam2 la plak. kena download kat sini la plak
baru la saya tahu yang laptop saya takder microsoft.NET 2.0. patut la masa install sap logon 7.1 cam haru-biru terus laptop saya. terpaksa fall back ke sap logon 6.4.
nak selesaikan masalah worm terjumpa solution untuk sap logon 7.1 plak. heheheheeh magik je kan….huhuhuhu
then terus la download microsoft.NET 2.0 kat sini and then install.
The Microsoft .NET Framework version 2.0 (x86) redistributable package installs the .NET Framework runtime and associated files required to run applications developed to target the .NET Framework v2.0.
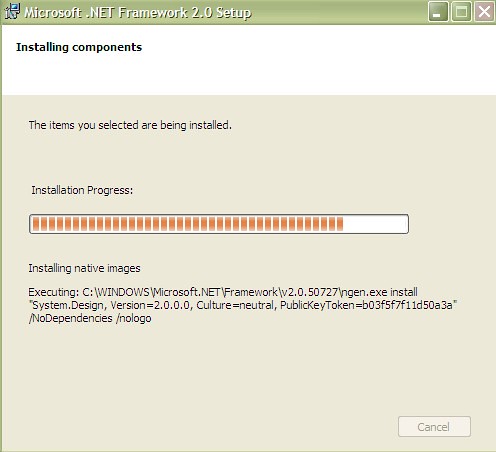
semua ok adjer. lepas install, run balik program worm removal tuh, then need to restart.
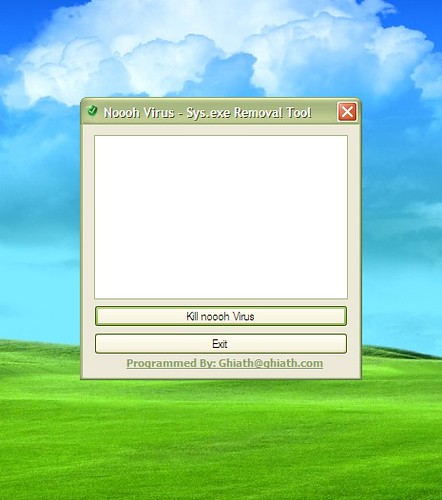
bila windows xp sp2 saya restart, semua nya ok.
dah takde lagi cacing2 pembawa malapetaka tuh semua.
saya dah berjaya bukak balik regedit ngan task manager saya!

hahahahaahah berjaya siot……. x ku sangka sesenang ni plak. huhuhuhu
discovered: September 18, 2001
Updated: February 13, 2007 11:55:03 AM
Type: Trojan Horse
Normally, this backdoor Trojan horse is distributed as one large installation executable. Once run, this executable pretends to install a benign antivirus program, while in the background it installs the backdoor files in various places on the system.The inserted files are:
- C:\Windows\DskLoad.exe
- C:\Windows\Prun.exe
- C:\Windows\Sys.exe
- C:\Program Files\Accessories\Backup\System\Critical\Cons1.dll
- C:\Program Files\Accessories\Backup\System\Critical\Deg326.dll
- C:\Program Files\Accessories\Backup\System\Critical\Expl32.exe
- C:\Program Files\Accessories\Backup\System\Critical\Explorer2.exe
- C:\Program Files\Accessories\Backup\System\Critical\ins.dll
- C:\Program Files\Accessories\Backup\System\Critical\Mir436.dll
- C:\Program Files\Accessories\Backup\System\Critical\Mirc.ini
- C:\Program Files\Accessories\Backup\System\Critical\Moo.dll
- C:\Program Files\Accessories\Backup\System\Critical\Mstg1.dll
- C:\Program Files\Accessories\Backup\System\Critical\Scan31.dll
- C:\Program Files\Accessories\Backup\System\Critical\Updatex1.dll
- C:\Program Files\Accessories\Backup\System\Critical\Win32x.dll
- C:\Program Files\Accessories\Backup\System\Critical\Winexp32.dll
- C:\Program Files\Accessories\Backup\System\Critical\Winvar32.dll
NOTE: Most of the .dll files in this list are not dynamic link libraries but are IRC script files and other data files.
All the files in the C:\Program Files\Accessories\Backup\System\Critical folder are created with “Hidden” attributes, in an attempt to escape being noticed. In order to gain control of the compromised system, this Trojan horse does the following:
- It modifies the run= line of the C:\Windows\Win.ini file so that it becomes:run=C:\Windows\DskLoad.exe
- It makes the following modifications to the registry:
- In the keyHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\mIRCit adds or modifies the valueDisplayName mIRC
- In the keyHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\mIRCit adds or modifies the valueUninstallString c:\program files\accessories\backup\system\critical\expl32.exe” -uninstall”
- In the keyHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Runit adds the valueStubPath C:\Windows\DskLoad.exe
- In the keyHKEY_LOCAL_MACHINE\Software\Microsoft\Active Setup\Installed Components\KeyNameit adds or modifies the valueMSSysDisk C:\Windows\DskLoad.exe
- Finally, IRC file extensions are hooked in HKEY_LOCAL_MACHINE\Software\Classes that call “c:\program files\accessories\backup\system\critical\expl32.exe” when chat files are opened.
The inserted file C:\Windows\Sys.exe is waiting for the user or a program to call the “sys” command. In DOS-based operating systems, the file Sys.com is used to make a data medium DOS bootable. On Windows computers, this file would reside in C:\Windows\Command\sys.com. However, when running “sys” from the command prompt, the viral C:\Windows\Sys.exe is run instead of the proper C:\Windows\Command\sys.com.
This viral sys.exe installs Backdoor.Subseven.22 on the system allowing for even more control over the compromised system.
Recommendations
Symantec Security Response encourages all users and administrators to adhere to the following basic security “best practices”:
- Turn off and remove unneeded services. By default, many operating systems install auxiliary services that are not critical, such as an FTP server, telnet, and a Web server. These services are avenues of attack. If they are removed, blended threats have less avenues of attack and you have fewer services to maintain through patch updates.
- If a blended threat exploits one or more network services, disable, or block access to, those services until a patch is applied.
- Always keep your patch levels up-to-date, especially on computers that host public services and are accessible through the firewall, such as HTTP, FTP, mail, and DNS services (for example, all Windows-based computers should have the current Service Pack installed.). Additionally, please apply any security updates that are mentioned in this writeup, in trusted Security Bulletins, or on vendor Web sites.
- Enforce a password policy. Complex passwords make it difficult to crack password files on compromised computers. This helps to prevent or limit damage when a computer is compromised.
- Configure your email server to block or remove email that contains file attachments that are commonly used to spread viruses, such as .vbs, .bat, .exe, .pif and .scr files.
- Isolate infected computers quickly to prevent further compromising your organization. Perform a forensic analysis and restore the computers using trusted media.
- Train employees not to open attachments unless they are expecting them. Also, do not execute software that is downloaded from the Internet unless it has been scanned for viruses. Simply visiting a compromised Web site can cause infection if certain browser vulnerabilities are not patched.
Writeup By: Andre Post
![]()


Pingback: noooh « Bersama Kongsi Ilmu